The funds industry is ramping up cyber security defences. Nicholas Pratt looks at what to do in the event of an attack.
In March, the Investment Association (IA), the trade body for the UK’s fund managers, announced the launch of IA Training, an online portal designed to give fund managers lessons in cyber security awareness.
Ten courses certified by GCHQ, a UK government intelligence agency, will cover a series of key topics including social engineering, removable media, remote and mobile working, personal devices and phishing – in other words, the technological advances that have made for a more accessible workplace but which have opened up a Pandora’s box for cyber security.
According to the IA, the new courses will help asset management staff to identify and minimise the risk from cyber threats. “Training employees to recognise and respond to risks is a key part of an asset management firm’s defence against cyber threats,” said IA chief executive Chris Cummings. “These threats are constantly evolving and it is vital that as an industry, we continually invest to protect our businesses and our customers from potential cyber-security breaches.”
Keeping up to speed
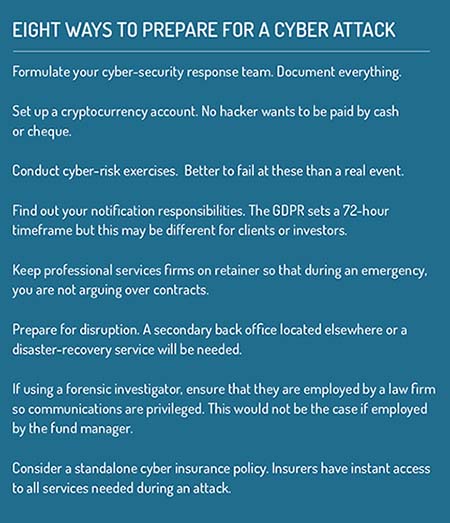
One catalyst for this cyber-risk education push is the imminent introduction of the General Data Protection Regulation, known as the GDPR, and its requirement that firms notify their regulators within 72 hours of a suspected data breach or cyber attack.
The other catalyst is the growing sophistication and diversity of the threat, which now ranges from ethically motivated hacktivism to criminals buying computer viruses on the dark web, to state-sponsored cyber attacks on critical infrastructure and supply chains.
There are several technology changes that fund managers need to make in order to keep up with the evolving threats. And not just tech, but culture, people and a firm’s own policies and procedures, says Matt Palmer, senior director for cyber risk management solutions at consultants Willis Towers Watson.
First, on the technology side, the rules-based tools that have formed the basis of most fund managers’ cyber defences need to be upgraded, says Palmer. “They are still of value but are nowhere near as sophisticated as they need to be,” he adds.
Consequently, there is now a greater use of artificial intelligence and machine learning in cyber security and antivirus software, indicative of a move away from a purely preventative approach to one based more on constant monitoring.
“Having the ability to detect and respond to ongoing attacks within an hour is critical for ensuring incidents don’t turn into breaches,” says Zeki Turedi, a technology strategist at antivirus software provider CrowdStrike.
According to CrowdStrike’s ‘2018 Global Threat Report’, the average “breakout time” (the time taken for an intruder to move from the initial compromised system to other places in the network) was just under two hours. At the same time, other cyber attacks can lie undetected for weeks or even months due to sophisticated malware that can be programmed to be activated some time after infiltration.
CrowdStrike’s report also highlighted the threat of attacks in software supply chains. Almost every organisation in the world relies on third-party software for a wide range of applications and many specialist applications may have been developed by smaller vendors that are not necessarily using what Turedi calls the “security development life-cycle process”, a protocol designed to ensure security compliance requirements are met during the development process.
It is a vulnerability on which attackers have sought to capitalise, says Turedi.
“Attackers are using the trust that we have in certain applications, either by setting up fake blogs in the name of a trusted vendor or by exploiting the vendor’s infrastructure, allowing them to send a malicious tool during the update of the app.”
For example, in 2017 a Ukrainian tax accounting app called M.E.Doc was compromised to deliver a virus called NotPetya which ended up taking down thousands of computers in more than 50 countries.
For fund managers, the issue is exacerbated by their own position in a complex supply chain involving large banks and custodians on one side, and small investors and suppliers on another.
Furthermore, fund managers have become increasingly visible in what is seen as a lucrative chain. And, says Willis Towers Watson’s Palmer, firms can no longer rely on attackers going after the banks instead of them.
“Years ago, fund managers would see themselves as out of the spotlight, but no one is off the hook,” he says. “Attackers are working down the supply chain and those behind the curve in terms of cyber security will be put under pressure from their partners to catch up with the leaders.”
Fund managers should also apply their own pressure on supply chain providers, says Jerry Norton, vice president of global financial services business at CGI, a business and IT consultancy. They should ensure there is a right of inspection and that tools are employed to inspect code. Third-party software should also be scanned and updates made securely.
Norton says fund managers must be prepared to stop dealing with a supplier or client if they do not have the requisite security clearance.
Insured risk
A likely consequence of pressure from supply chain partners and the GDPR could be the greater take-up of cyber insurance. At some point a client, supplier or regulator is likely to insist on some form of cyber-risk protection.
 This market is still in its infancy in Europe and not without shortcomings. Typically, insurance deals with physical risks and pricing is based on years of historical loss data. There is also the assumption that low-risk insureds (good drivers, for example) will subsidise the higher-risk insureds (bad drivers) in the same pool. In the cyber-risk world, none of these principles apply.
This market is still in its infancy in Europe and not without shortcomings. Typically, insurance deals with physical risks and pricing is based on years of historical loss data. There is also the assumption that low-risk insureds (good drivers, for example) will subsidise the higher-risk insureds (bad drivers) in the same pool. In the cyber-risk world, none of these principles apply.
Consequently, many consider current premiums too high and the coverage limits too low, but insurers are looking to be more innovative and offer standalone cyber policies that not only cover the cost of recovery but also include access to the third-party services needed in the event of a cyber-risk attack.
“If you do not have cyber cover, you can be left with very high costs, so it does make sense to have some form of risk transfer in place,” says Palmer.
“It is important to talk to your broker and ensure there are no gaps in coverage or that you have the appetite to manage those exposures in-house. Plus, firms must remember that insurance is not a substitute for risk management or for a professional cyber response plan.”
This article first appeared in Funds Europe
©2018 funds global mena